If someone has access to your IP address and wifi network info, can they remotely access devices that are connected to that wifi network, and how would you know if they were
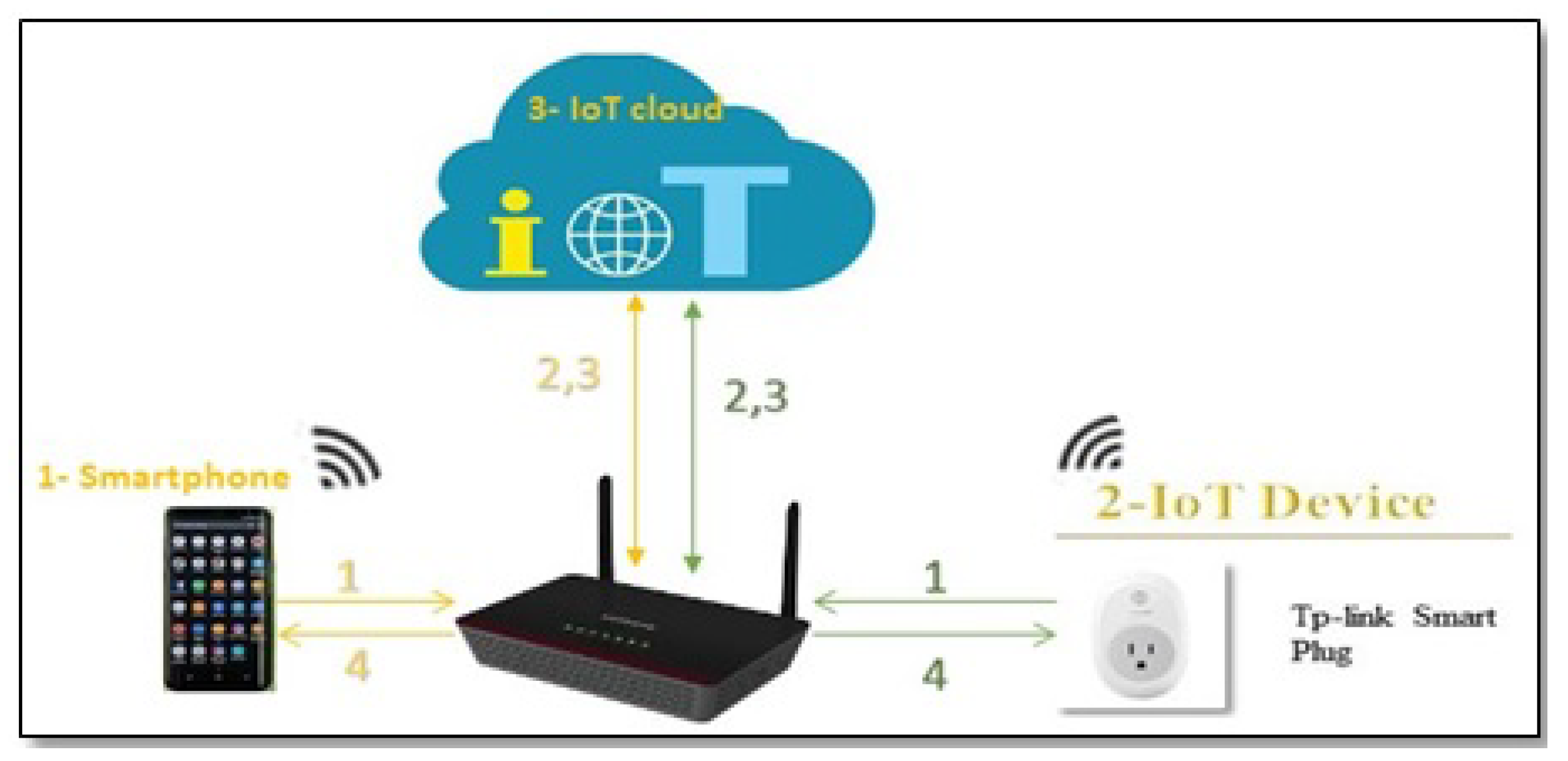
Sensors | Free Full-Text | Detecting IoT User Behavior and Sensitive Information in Encrypted IoT-App Traffic | HTML
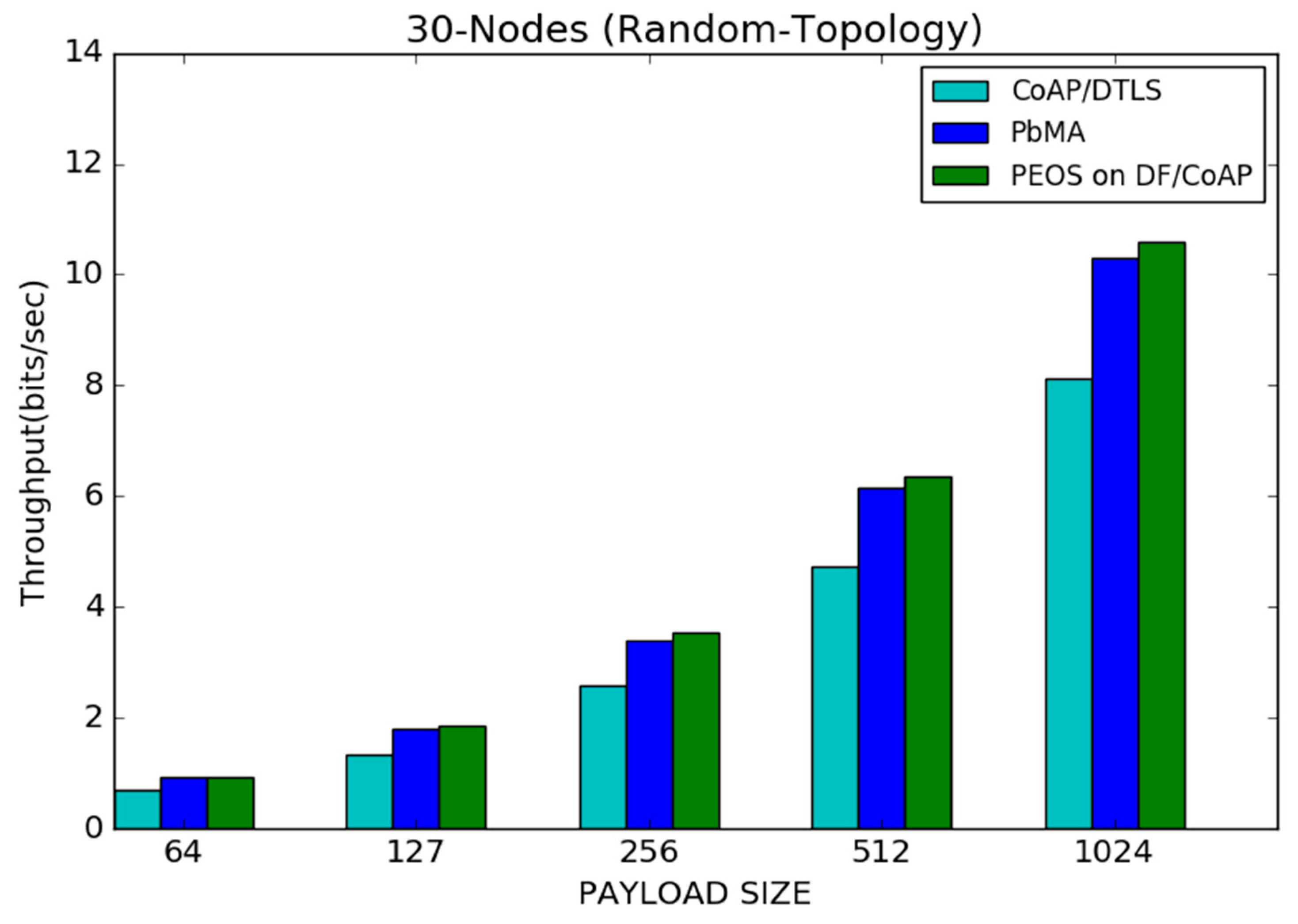
Sensors | Free Full-Text | Lightweight Payload Encryption-Based Authentication Scheme for Advanced Metering Infrastructure Sensor Networks | HTML
![2020 Henry Schein Dental Merchandise Catalog (without pricing) [960 - 961] 2020 Henry Schein Dental Merchandise Catalog (without pricing) [960 - 961]](https://nxt-staging-books.s3.amazonaws.com/nxtbooks/henryschein/merchandise2020_nopricing/iphone/page960_conv_hires.jpg?1592203798)
/how-to-properly-restart-a-router-modem-2624570-8ef8d3ea41a14c928947e58c32fa3646.png)